1. Select a discrete app icon.

notes
A Guide to Cyberstalking
A look at the tactics cyberstalkers use—from hidden trackers to hacked smart homes—and the steps you can take to protect yourself
- Apr 13, 2026
Technology has given us many gifts: Navigation that reroutes us around traffic, phones that unlock with our faces and the ability to store our entire lives—photos, messages, calendars—inside a device that fits in a pocket.
Unfortunately, that same technology can also hand powerful tools to someone who wants to stalk, monitor or control a partner. And it can seem like every day brings a new device or app that, in the wrong hands, becomes another tool for abuse.
Fifteen years ago, security expert Robert Siciliano said stalking via cell phones was a relatively new issue that people were just beginning to understand. At the time, Siciliano had spent more than 30 years as a private investigator before founding the cybersecurity training company Protect Now.
“Spyware was a consumable product meaning you could buy software you could install on a device that would provide unfettered access to that device,” he says. It would take somewhat of a tech expert to do that. But nowadays, it’s as simple as downloading an app on a partner’s phone while they’re unaware.
From there, says Siciliano, a perpetrator can remotely control the device.
“They can make phone calls from it remotely. Listen to the ambient audio that the microphone picks up. Listen to the phone calls as they are in play. They’re able to see all the media on the phone—text messages, pictures, videos,” he says.
- Is Cyberstalking Illegal?
- Why Am I Being Cyberstalked?
- What Does Cyberstalking Look Like?
- How to Recognize Spyware
- How to Be Safe Online
- The Difference Between Cyberstalking and Cyberbullying
- Online Protections if You’re Still With an Abuser
Is Cyberstalking Illegal?
Yes. Is it hard to prove? Also, yes. Which is a fact abusers rely on. Further down,, we’ll talk about how to gather the most evidence to help your case.
While stalking is illegal in all 50 states, the specific nuances of each stalking law vary, including how cyberstalking is described. You can find out how your state defines stalking here. Luckily, the Violence Against Women Act enacted a cyberstalking amendment to the federal criminal provisions against stalking in 2013. It states that using electronic communication to cause a person “reasonable fear” of death or serious bodily injury, or that causes emotional distress, is illegal and punishable by up to five years in prison or a $250,000 fine.
Why Am I Being Cyberstalked?
Most cyberstalkers, like other stalkers, are known to the victim—often a current or former partner. In some cases, they may be an acquaintance or even an obsessed stranger. Researchers say there is a difference between those who cyberbully and those who cyberstalk. As a 2022 study states, “Cyberbullies are not so much interested in the person they are bullying but rather in the act of bullying itself, the opportunity to assert their power over the victim in general. The cyberbullies also need an audience, onlookers who applaud their behavior. The cyberstalker, on the other hand, harasses the victim with the intention of restoring or establishing a love relationship.”
“Winning back” an ex-partner through relentless harassment or threats is one motive of a cyberstalker, but there are also several others, say experts:
- To demean, embarrass or scare someone.
- To track someone’s whereabouts without them knowing.
- To damage a person’s reputation.
- To get someone fired from a job or kicked out of school, sometimes as a form of financial control.
- To make unwanted sexual advances.
- To steal someone’s identity or impersonate them online.
In order to do this, there are many disturbing ways the cyberstalker goes about it.
What Does Cyberstalking Look Like?
There are many ways abusers have learned to automate stalking, says Siciliano. These are some of the most common.
AirTags
There are all sorts of low-cost Bluetooth-enabled trackers on the market these days, and abusers are known to hide them in cars, purses, the lining of jackets and kids’ backpacks in order to stalk their victims. Apple’s AirTags, introduced in 2021 for the very accessible price of just $29 might be the most familiar.
Stories of women being stalked by current or former partners through the use of AirTags are plenty, from an Indiana man arrested after his ex-girlfriend was notified of an unfamiliar AirTag on her car, to a Miami-Dade police officer who did the same thing in order to stalk his ex-girlfriend.
At least 37 people joined a class-action lawsuit filed in 2022 against Apple claiming their product has become “the weapon of choice for stalkers and abusers.” The suit is still ongoing. However, Apple did make a concerted effort to make stalking less likely using AirTags by partnering with Google in 2024 to implement a cross-platform unwanted tracker alert. Alerts of unknown AirTags now appear within a few minutes rather than hours and iOS now scans for any unknown trackers, not just AirTags.
Stalking can and does often escalate to other forms of power and control, including violence and even homicide. That’s why some people refer to stalking as “murder in slow motion.”
“In 85 percent of attempted and 75 percent of completed femicides there has been an episode of stalking within the year prior to the murder,” says Jennifer Landhuis, director of SPARC, the Stalking Prevention and Awareness Center. “Stalking produces a three-fold risk of intimate partner homicide, meaning if a victim of domestic violence is also being stalked, they are 300 percent more likely to be killed by that intimate partner.”
And it’s not just women in danger. In 2022, a man was run over and killed by his ex-girlfriend after she used an AirTag to track his location and suspected he was cheating.
While Apple has stated publicly that its devices are designed to track belongings, not people, and that they condemn malicious attempts to use AirTags, many argue that the notification system of an unknown AirTag needs improvement. Currently, it can take up to eight, sometimes 24 hours, for a user’s phone to ping them with an alert that an unknown AirTag is traveling with them. And if you don’t hear that ping, the AirTag could continue traveling with you until you glance at your phone.
“This type of technology is absolutely being misused to perpetrate acts of modern gender-based violence,” says Adam Dodge, a California-based attorney. Dodge founded the nonprofit EndTAB in 2019.
While cases like this are extreme, they underscore a growing problem: small tracking devices can be used to secretly monitor someone’s movements. The good news is there are ways to detect them.
You’ll likely get an alert that an unknown AirTag is “moving with you” if someone has put a device on you without your knowledge. You have an option at that point to have the AirTag play a sound to help you locate it.
If you tap on “Learn About This AirTag,” you can check its serial number to see if it’s been reported lost and, if so, find instructions for getting in contact with the owner. (Be wary of this if you have any suspicions that you might be being stalked. If in doubt, return the AirTag to an Apple store.)
If the AirTag was not reported lost and you don’t know where it came from, tap on “Disable AirTag” and follow the steps to prevent it from continuing to track your location, which will include removing its battery.
If you can’t find the AirTag, search all of your belongings or wait to see if another notification pops up (there is a chance the AirTag is no longer with you). If the AirTag is away from its owner for 8 hours (up to 24 hours), it will begin regularly emitting a ping, which could make it easier to find.
An AirTag may have wound up with you for a harmless reason, or it could be a red flag-level threat, says security expert Spencer Coursen, author of The Safety Trap. In the latter case, Coursen’s willing to bet you already know who did it.
“Think about who had access. It’s going to be a pretty limited pool. And it’s likely going to be exactly who you think it is.”
You can report AirTags or other stalking behaviors to the police, but don’t try to engage with a stalker directly. They’re looking for a response, which often only ramps up their efforts to stay in contact with you.
Spyware/Stalkerware
Spyware, also called stalkerware,, is any kind of stealth app that abusers install on your phone that are completely hidden. The abuser can then mirror every text, keystroke and photo to a remote dashboard without an icon appearing on the victim’s home screen, says Siciliano. They can also see your phone’s location, monitor what you’re looking for online, record your phone conversations and some advanced spyware can even hijack phone calls, meaning that calls coming into the victim’s phone will be rerouted to the abuser’s phone. And likewise, the abuser can make phone calls that appear as though they’re coming from the victim’s phone.
Maybe most frightening, spyware can even tap into a user’s phone or computer camera to spy on a victim, or access the microphone to monitor ambient sound without the victim knowing.
The same kind of stalkerware can be installed on a victim’s computer or laptop as well, and perform all of the same functions, hijacking email and remotely turning on the computer’s camera to spy on the victim.
Even without the installation of spyware, abusers can still monitor someone’s activity and whereabouts if that person is using social media. When we take photos with our phone, metadata is embedded in the photograph with details including the date, time and exact location of where it was taken. Our phones are automatically set to have geolocation turned on and a lot of people don’t realize this. While most social media platforms automatically remove this embedded data for safety reasons, it’s still worth noting. Your location can still be determined through captions, check-ins, visible landmarks and other contextual clues. Read “8 Tips for Social Media Safety” to learn more.
Family-Plan Surveillance
Imagine sharing a phone plan with someone who can quietly see more than you realize. They can check who you’ve called or texted, look at your billing details, and in some cases even see where you are. Nothing about it looks like hacking—it’s all built into the account. But in the wrong hands, those everyday features can turn into a way to keep watch. An abusive partner might notice new numbers, track your movements, shut off your service or question you about where you’ve been. And because it’s all happening through normal account access, many people don’t realize it’s even possible.
Data Broker Exposure
For a survivor trying to disappear—or at least create some distance—it can be made more difficult if your information is still out there, scattered across the internet. This one isn’t so much abuser-driven, but rather something abusers can access. Data brokers collect and sell personal details pulled from public records, apps, purchases and online activity. They build profiles that can include where you live now, where you used to live, your phone number, your relatives, even where you work. Someone looking for you doesn’t need special skills to find it—just a search box or a small payment for a report. Because this system operates quietly and legally, most people have no idea how visible they are—until that visibility becomes a risk.
Hacking Homes’ and Cars’ Tech
High-tech homes and cars don’t know the difference between us and someone pretending to be us, which can be an obvious problem. And today’s homes are full of smart devices like thermostats, fridges, video doorbells, camera-enabled security systems, and voice assistants like Alexa and Echo that control everything else while also telling us the weather each morning.
Attorney Alexis Moore, cyberstalking expert, risk management consultant, survivor and author of Surviving a Cyberstalker, says her clients have reported things like an abuser who would remotely turn on the heat in the survivor’s house on the hottest summer days via her smart thermostat just to unnerve her and remind her he was in control.
Another abuser would repeatedly unlock a survivor’s home and car doors remotely. When the survivor tried to report it, the abuser petitioned the judge in their children’s custody case that this was a security issue he was worried about, making the survivor appear as an unfit mother.
Another abuser would unlock a survivor’s electronic front door, go inside and take just one item from her home at a time, like a bracelet or a pair of shoes. The survivor kept thinking she was losing things and her mind along with them. She knew reporting these missing items to the police without any proof of a break-in would sound outrageous.
There are also reported incidents of abusers listening in through survivors' smart TVs, devices like the Amazon Alexa or Echo, or Wi-Fi-enabled home security cameras. Those who are tech savvy can figure out how to use them as built-in spy devices, says Moore, eavesdropping on conversations in whatever room of the home these devices are placed in and then using that information to stalk, threaten or intimidate a survivor.
Abusers have also been known to take advantage of smart cars' GPS systems and cameras as another tool in their stalking toolbox. The savvy stalker can hack into these systems, or learn the password from a current or former partner, and log in as the driver. The stalker will be able to know every place a victim goes and when they leave and arrive home. A stalker could even reroute the victim’s GPS as a type of mental torture.
While some of these offenses might sound tame compared to more violent types of abuse, Moore says this sort of control can cause real trauma, especially since the survivors often struggle to find anyone who will believe them.
“It’s meant to psychologically torment,” says Moore, who adds that abusers are savvy enough to know that most of these stalking-type incidents will not be taken seriously by law enforcement.
Oftentimes, these things often go hand-in-hand with other types of abuse or child custody battles, with the abuser tormenting the protective parent before court as to make them rattled. Sometimes, says Moore, the abuser will pin the survivor as someone who is mentally ill, a claim the judge may consider when she says lights flicker in her home for no reason,at all hours of the day and claims her estranged partner is to blame.
AI Voice and Deepfake Spoofing
As Siciliano says, “AI is making everything better and everything worse. It’s an amazing tool that can be abused like any other tool that’s ever been introduced.”
Over the past several years, there has been an undeniable uptick in AI technology being used for nefarious purposes. Stalkers use it to create fraudulent audio or video of a victim for the purposes of shaming, embarrassing or blackmailing them. Often these AI-created videos and images are sexual in nature and are referred to as deepfake revenge porn. They may be shared out of spite after a victim leaves or as a means of control to keep a victim from leaving.
It should be noted that revenge porn also encompasses non-AI-created sexual images or videos taken with or without consent that the abuser then threatens to release if the survivor doesn’t do as they say.
Siciliano says AI technology can also be used by stalkers to mimic the victim’s voice as a way to manipulate friends, family members or employers into revealing the victim’s location.
How to Recognize Spyware
If you know that a current or former partner is stalking you, there is a good chance spyware/stalkerware is being utilized in some way. But there are clues to look for as well.
- Your phone or computer is behaving strangely. If you notice ongoing oddities, such as the phone lighting up or turning off by itself, it may be spyware running in the background. Another indicator is difficulty shutting your phone off or a lengthy delay when shutting it off. Once isn’t an indicator, but if it happens consistently, it might mean a tracking app is present.
- The person you suspect of stalking you knows too many details about you, such as where you are (and you didn’t tell them), who you’ve been texting or talking to or specific things you’ve searched online.
- Your phone battery is being drained more quickly than it used to even though you haven’t changed any settings or installed any new applications. Spyware runs constantly, so it could be eating up battery life. Note: Newer spyware doesn’t use as much battery power as older or less-sophisticated programs, so don’t rule out spyware being present just because battery life seems normal.
- There is consistent background noise on calls. Some spyware automatically records phone calls and can lead to additional background noise or a sound that mimics a bad connection. Of course, bad connections are real, so don’t assume spyware is present if it happens only every once in a while. But if background noise, echo or static is present on every call you make, your calls might be being monitored.
- You’re getting random, nonsense text messages. If you receive text messages that are a jumble of numbers or other characters from an unknown number that make no sense to you, your phone likely has been hacked. These messages are the spyware sending code to the phone to perform tracking tasks.
What To Do If You’re the Target of Cyberstalking
Cyberstalking can feel overwhelming, but there are practical steps you can take to protect yourself and start building a record of what’s happening.
- Don’t reply. Online or in-person, most stalkers thrive off engagement from their target. As tempting as it might be to send an angry all-caps text to leave you alone, don’t. It’ll only encourage the stalker to continue their communication.
- Start keeping a paper log of everything you notice related to the cyberstalking. Note any compromises to your personal information, any ways in which your devices are acting strangely and any ways the suspected stalker shows up in your life.
- Take your device to a tech expert and ask them to check it for spyware. If you find it, note what it is and then consider doing a factory reset of the device, which should wipe out spyware. Use antivirus or anti-malware software that can do regular sweeps of your device for potentially harmful applications.
- Some auto mechanics are also able to do a sweep of your car for tracking devices. If you find a tracker on your car, take photos of its placement before removing it and reporting it to police. Police are likely to take the device as evidence but make sure you ask for a copy of their report that inclueds the device’s serial number and location.
- Contact law enforcement. Show them the evidence of cyberstalking and especially highlight any threats to your safety or ways in which the cyberstalking is causing emotional distress. Statements like, “I know where you live” or “I am watching you,” are threats to your safety. Consider filing for an order of protection if you know who the stalker is.
Remember that tipping off your stalker by deleting the spyware or tracker could put you in more danger. It’s also helpful to consult with a domestic violence advocate and develop a safety plan.
How to Be Safe Online
Unfortunately, it’s not that difficult for a cyberstalker to access someone’s information online or hack into a smart device. If you’ve ever Googled yourself before, you know how much so-called private information can be found just by searching for a name. That’s why it’s important to take safety precautions any time you go online or add new technology to your life. Think of it as virtually locking your front door.
- Don’t overshare. To be cautious, consider anything you put online to be public information, privacy settings or not. Think about what you post and whether or not a stalker could potentially use that as leverage. This includes your address, your children’s names, a picture of the front of your home or your car, where your kids go to school, your place of work or the fact that you just left for a week-long vacation.
- Monitor your children’s social media. Set up rules ahead of time to keep them safe—maybe it’s that you get to see their activity, messages or photos. Or their account is linked to yours. Consider times and places where technology can be accessed. Keep an open communication about why it’s important to be safe online and the dangers that exist. You may want to consider an app like Life360 or Bark to help monitor their online activity. Some providers have free programs built into their applications or platforms, such as Google’s Family Link.
- Hide your IP address. An IP address can reveal your approximate location and internet provider, which may let a cyberstalker narrow down where you are or attempt certain online attacks.Learn how to hide your IP address here.
- Turn off geotagging. When we take photos with our phone, metadata is embedded in the photograph with details including the date, time and exact location of where it was taken. Our phones are automatically set to have geolocation turned on and a lot of people don’t realize this. Here’s information about turning off geotagging on your iPhone and iPad, and information about turning it off on Android devices.
- Promote a business, not yourself. You might have to make a public profile if you have a business that needs an online presence. In that case, make sure your business is the focus, not you. Keep the business address private (secure a P.O. Box instead of listing a street address) and create an email address that doesn’t include your name. Keep your name and personal information off the page and don’t hesitate to use a plural “We” when talking about your company or product, even if you’re the sole employee. It will be less alluring for a stalker to harass an entire company than one person.
- Pick a vague nickname. If you’re on a dating or other social app, pick a nickname that’s vague, not a spin-off of your real name or exact location. Same thing if you’re leaving comments on a message board or blog. Instead of “AndreainTopeka” choose something like “MidwestMom29.”
- To prevent your Smart Home devices from being hacked, the most obvious answer is to not use those devices. But if you are going to, this piece delves into ways you can strengthen the safety of these devices.
The Difference Between Cyberstalking and Cyberbullying
Cyberstalking is a type of cyberbullying, but cyberbullying can include a lot more ways to harass and threaten a survivor. Many of those ways don’t involve any hacking at all. Here are some tactics of cyberbullying that abusers may also utilize:
- Defamation: An abuser posts lies about an individual in an attempt to disparage his or her character.
- Doxxing: An abuser posts an individual’s private information, including full name, address, date of birth or social security number with the intent of harassing the individual or opening them up for others to commit crimes against them.
- Google bombing: In this tactic, the perpetrator uses optimization to cause defamatory content to rise to the top of search results when someone Googles the victim’s name.
- Online impersonation: This is when an abuser creates a fake account or hacks into a victim’s account and sends messages that appear to be coming from the victim. Often the messages are disparaging or defamatory in nature. Or, they may be used to cause turmoil between the victim and a third party. In extreme cases, abusers post fake sex work ads or rape fantasies inviting individuals to the victim’s home for sex.
- Revenge porn: An abuser shares intimate photos or videos of a sexual partner that were obtained with or without consent during the relationship or when the abuser hacked into the victim’s computer, phone or online document storage. This can also be referred to as sextortion, and it’s become a targeted problem for teens.
- Stalking a Victim’s Location: Abusers tracking the victim’s whereabouts through online “check-ins” or by installing GPS tracking on the victim’s phone and monitoring the location hits.
- Threatening: This tactic is as old as time but can now be done behind a veil of secrecy. Internet threats aren’t always taken seriously by online platforms or law enforcement but they do cause real anxiety in victims.
- Unsolicited pornography: This occurs when an abuser sends unwanted pornography to a victim or posts it online, such as in an open-forum comment. It also includes sexualizing a photograph of the victim and posting it online.
You learn about even more, nuanced types of cyberbullying at the Women’s Media Center.
Online Protections if You’re Still With an Abuser
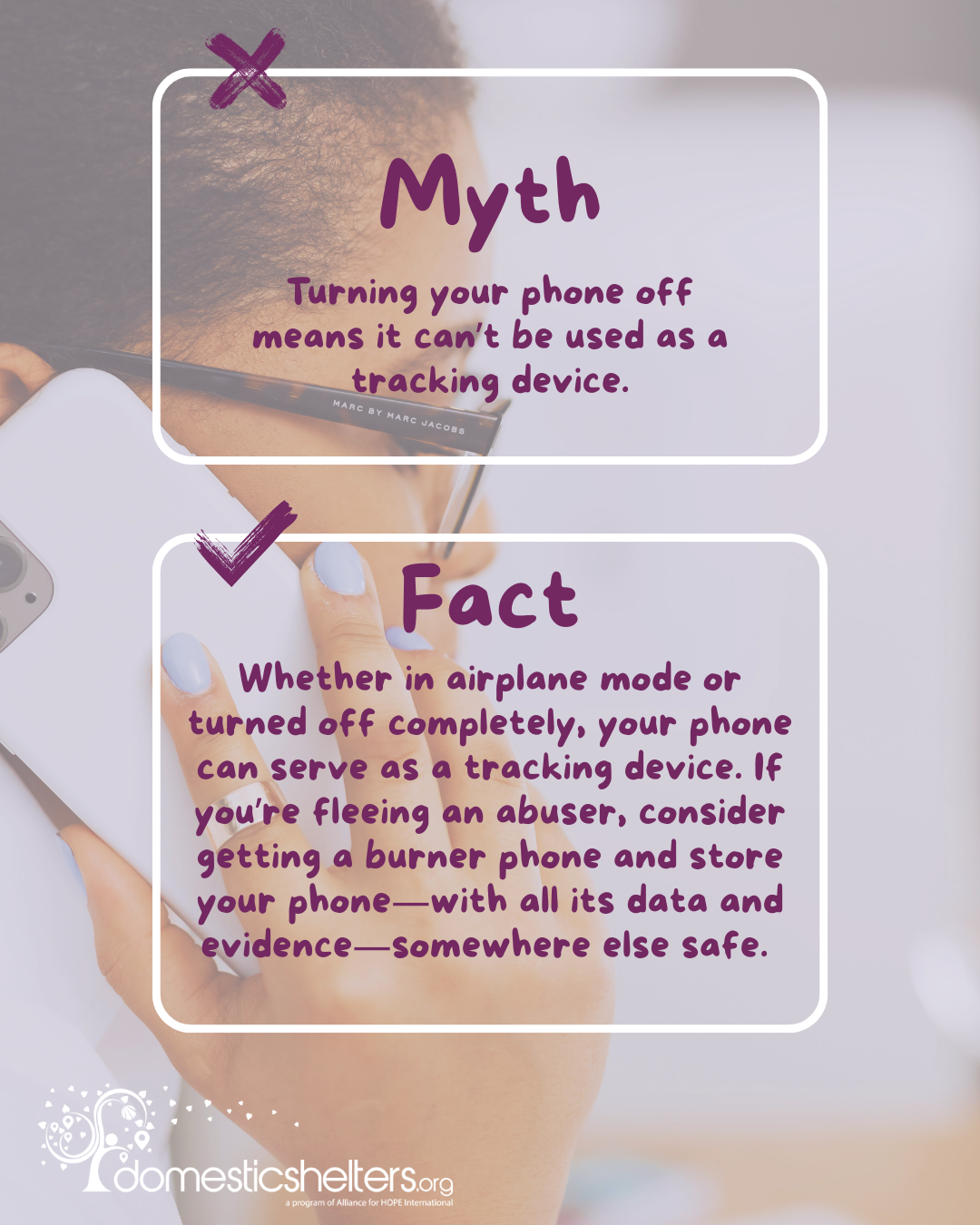
If you’re a victim of domestic violence who is still living with an abusive partner, extra precautions online should be considered, especially if you’re looking for information or help to escape. Try to use a computer or phone that isn’t your’s, if possible, to research domestic violence or chat online with an advocate. Try the library, a friend’s house or your workplace. Disable texts and emails from popping up on your screen to avoid sensitive information being seen by an abuser. And keep in mind that a phone, even in airplane mode or turned off completely, can serve as a tracking device. If you’re fleeing an abuser, consider getting a burner phone and store your phone—with all its data and evidence—somewhere else safe.
I would advise that they download all the info, contacts and data they need if they decide to switch phones. Or they could turn it off, keep it and add a new one they use in the future, keeping the information they have built into their phone accessible. Tech help to disable spyware or tracking devices before they silence it is critical, so if they activate it for information, it won't reveal where they are now.
Remember: Any cell phone that can be turned on and can connect to a current network can call 911, even when it is not activated and even if the account has lapsed due to late or no payment. Just be mindful, as many older phones can’t connect to a current network and call 911 since U.S. carriers shut down 3G networks in 2022.
Cyberstalkers rely on their threats to keep victims silent and isolated. If you believe someone is monitoring or harassing you online, consider reaching out to a domestic violence advocate or speaking with Hope Chat in the corner of your screen. Support and resources are available.
Donate and change a life
Your support gives hope and help to victims of domestic violence every day.







